A pretty serious security issue within
GMail was disclosed last week. I could explain the details, but odds are you don't care. If you do, check out
these posts from Ryan
Naraine. Suffice it to say, an attacker could direct you to a website that would inject code into your browser to add a
GMail filter to redirect your email.
Right, you want it in English. Basically, if you go to a bad web page, someone could have all of your email forwarded to them. Right, all of it.
What's the risk? What if you have bank account information or have to do a password reset. Or have some other sensitive or private information in email. You wouldn't be alone - Security Mike sure does. But I don't use a
webmail system for my most sensitive stuff.
This is where the post normally would stop, since I've told you about the issue and directed you to a few resources to go fix it. But since Security Mike's Portal is not going to be operational until October 15, I'll give you the fully
monty.
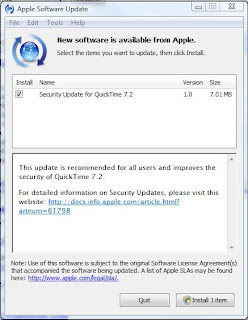
First of all, you need to make sure your
GMail isn't forwarded anywhere else. Hit "Settings" in the upper right hand corner of your screen. Then "Forwarding and POP" under the "Settings" tab. Here is the tab/screenshot to show that.
 Click on the image for a larger version
Click on the image for a larger versionThe key here is to have no surprises. If you have set up a forward on your account, that's fine. But an unexpected forward is bad. That's what you are looking for.
Next make sure there are no unknown filters. Again, hit "Settings" in the Upper Right Hand Corner, and then "Filters." You see I have no filters set up, so I'm OK. If you have already set up filters (as you can see I don't use
GMail too much), that's fine. You just want to look for strange filters that you HAVE NOT set up. Get rid of those if they are there.

You should be all set. Checking your forwarding and filters is a good thing to do every so often (every day for the next week, then maybe once a week). Remember, if someone owns your email, they pretty much own you.






























 tall Symantec and McAfee (without killing your machine)." Since a hallmark of Security Mike's approach is that consumers don't need to pay for security software anymore, you'll want to get rid of those heavy "suites" that slow down your machine and lighten your wallet. This report shows you how to do that.
tall Symantec and McAfee (without killing your machine)." Since a hallmark of Security Mike's approach is that consumers don't need to pay for security software anymore, you'll want to get rid of those heavy "suites" that slow down your machine and lighten your wallet. This report shows you how to do that.